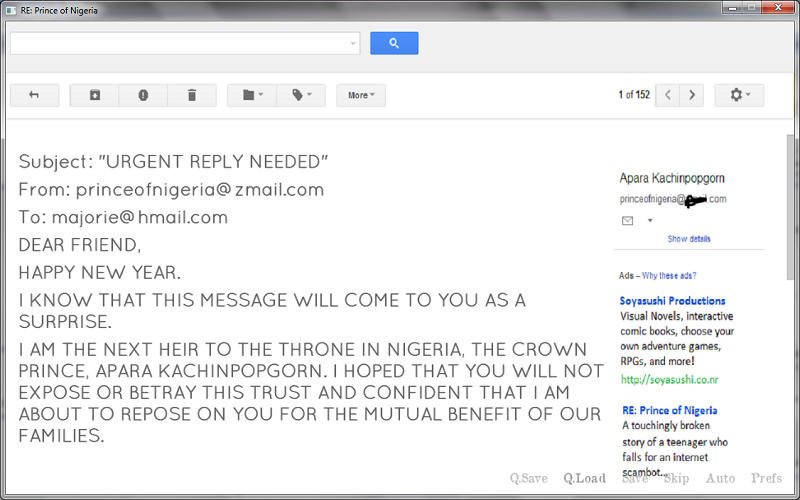
If you received one of the “Nigerian Prince” scam emails in the earlier days of the internet, you may have been left wondering who exactly falls for those things. The story was implausible and the grammar was terrible. But the reality is that today’s scammers are far, far more creative when it comes to building a scheme that people will fall for.
Here are just a few recent phishing emails that demonstrate how sophisticated these attacks have gotten.
Executive Email Account Hijacking
After gaining access to an executive’s email account, cybercriminals spent two weeks studying the executive’s emails to learn about the company’s financial processes. They also set up elaborate email rules to ensure certain emails wouldn’t reach the inbox. When a $15 million transaction was being discussed, they inserted themselves into the conversation, requesting the money be deposited in a different bank account instead. The email rules hid this conversation from the executive for two weeks – long enough to move the money to other accounts without arousing the banks’ suspicion.
Cyberattacks Pose as Cybersecurity Training
A scammer recently sent an email designed to look just like reminders for upcoming cybersecurity trainings. The email even specified that the next training wasn’t available on the company’s training portal, but required following a link in the email. The link, of course, was to a bogus site that requested login information to continue. Anyone who filled out the form gave their information to the cybercriminals.
Spoofing the Company Website
A phishing campaign last month loaded the target’s company website in the background when an email link was followed, and placed a Microsoft login prompt on top of the image. The user wasn’t actually on their company’s network, however – the fraudster was just pulling that content into their own website to make employees think the prompt was legitimate.
What Can You Do to Further Protect Your Business?
The reality is that some of 2020’s phishing schemes are so elaborate that they’re likely to snare at least a few employees. While user training remains a valuable tool to prevent employees from falling for scam emails, it’s difficult to teach every employee to keep their guard up enough to avoid a well-targeted scheme. One of these scams even came from a known email address.
This makes it more important than ever that businesses ask some uncomfortable questions:
- — If an employee does accidentally provide their credentials to a criminal, how much data will they be able to access using the credentials?
- — What processes are in place to detect unusual network activity and lock a user’s account?
- — How long will processes take to work?
- — Can data be restored if it was deleted?
Access prevention is still a key goal of any network security plan, but companies need to put additional protections in place between a “validated” user and the company’s most sensitive data.
To learn how modern cybersecurity strategies can help mitigate these risks, call us at (919) 600-5190 or visit https://www.wingswept.com/managed-services/cyber-security/.